Title: Default app for checksums with standard install?
Post by: pTeK on May 19, 2024, 04:29:19 AM
Post by: pTeK on May 19, 2024, 04:29:19 AM
Hi.
What is the default Nextstep 3.3/Openstep 4.2 app for a checksum?
Is there anything better than the default 16-bit crc /usr/bin/sum?
I believe the /NextAdmin/Installer.app/Installer does a 32bit checksum?
Also if any of you unix wizards can suggest a default installed app that can do a binary patch? i.e hex edit a PCI "Auto Detect ID" from inside a binary?
Thanks.
What is the default Nextstep 3.3/Openstep 4.2 app for a checksum?
Is there anything better than the default 16-bit crc /usr/bin/sum?
I believe the /NextAdmin/Installer.app/Installer does a 32bit checksum?
Also if any of you unix wizards can suggest a default installed app that can do a binary patch? i.e hex edit a PCI "Auto Detect ID" from inside a binary?
Thanks.
Title: Re: Default app for checksums with standard install?
Post by: nuss on May 19, 2024, 01:42:20 PM
Post by: nuss on May 19, 2024, 01:42:20 PM
Hi pTeK,
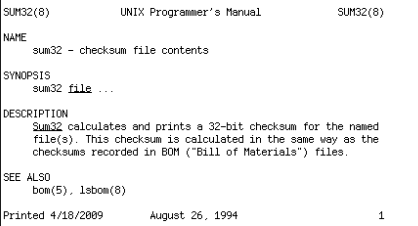
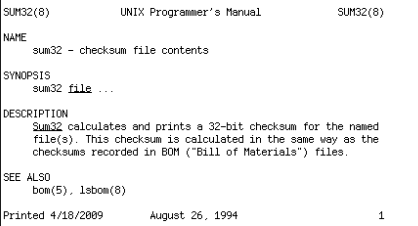
for your first question you can checkout /usr/etc/sum32, which exists hopefully in base-install.
Cheers
for your first question you can checkout /usr/etc/sum32, which exists hopefully in base-install.
Cheers
Title: Re: Default app for checksums with standard install?
Post by: pTeK on May 20, 2024, 04:35:54 AM
Post by: pTeK on May 20, 2024, 04:35:54 AM
Quote from: nuss on May 19, 2024, 01:42:20 PMHi pTeK,
for your first question you can checkout /usr/etc/sum32, which exists hopefully in base-install.
Thanks @nuss /usr/etc/sum32 is in both NS3.3 and OS4.2 :)
Now to find a way to binary replace 3 doublewords (3*4 bytes) with the standard tools.
Title: Re: Default app for checksums with standard install?
Post by: stepleton on May 20, 2024, 12:24:32 PM
Post by: stepleton on May 20, 2024, 12:24:32 PM
in the worst case, if you want to replace the longword at byte offset 1234 (decimal) with the string "hams", you can do something like the following. Note that you must be using the sh shell (not csh) for this to work on the NeXT. (It's probably a lot easier to put all of this stuff in a shell script anyway.)
$ dd if=original.file of=hacked.file bs=1 count=1234
$ echo -n '\0150\0141\0155\0163' >> hacked.file
$ dd if=original.file bs=1 skip=1238 >> hacked.file # note offset, also NeXT dd lacks conv=notrunc
Note how I've used octal to specify the bytes in "hams". I'm not sure how to do sh string escapes for hexadecimal in the sh that's available on NS3.3.
With combinations of count= and skip= arguments you can take out chunks around any run of bytes you want to modify. It's tedious but it will work.
Alternatively you could write yourself a little C program to do the patch.
It may even be possible to use dd to patch bytes within the target file itself, but I don't know dd well enough to do that!
$ dd if=original.file of=hacked.file bs=1 count=1234
$ echo -n '\0150\0141\0155\0163' >> hacked.file
$ dd if=original.file bs=1 skip=1238 >> hacked.file # note offset, also NeXT dd lacks conv=notrunc
Note how I've used octal to specify the bytes in "hams". I'm not sure how to do sh string escapes for hexadecimal in the sh that's available on NS3.3.
With combinations of count= and skip= arguments you can take out chunks around any run of bytes you want to modify. It's tedious but it will work.
Alternatively you could write yourself a little C program to do the patch.
It may even be possible to use dd to patch bytes within the target file itself, but I don't know dd well enough to do that!
Title: Re: Default app for checksums with standard install?
Post by: pTeK on May 20, 2024, 01:44:36 PM
Post by: pTeK on May 20, 2024, 01:44:36 PM
Quote from: stepleton on May 20, 2024, 12:24:32 PMin the worst case, if you want to replace the longword at byte offset 1234 (decimal) with the string "hams", you can do something like the following. Note that you must be using the sh shell (not csh) for this to work on the NeXT. (It's probably a lot easier to put all of this stuff in a shell script anyway.)Thanks @stepleton I forgot about using /bin/dd to copy sizes. Will probably look into using your way as it will be easier for scripting.
$ dd if=original.file of=hacked.file bs=1 count=1234
$ echo -n '\0150\0141\0155\0163' >> hacked.file
$ dd if=original.file bs=1 skip=1238 >> hacked.file # note offset, also NeXT dd lacks conv=notrunc
Note how I've used octal to specify the bytes in "hams". I'm not sure how to do sh string escapes for hexadecimal in the sh that's available on NS3.3.
With combinations of count= and skip= arguments you can take out chunks around any run of bytes you want to modify. It's tedious but it will work.
Alternatively you could write yourself a little C program to do the patch.
It may even be possible to use dd to patch bytes within the target file itself, but I don't know dd well enough to do that!
*ugh* octal, prefer hex, I guess that was the system I learned on the Amiga using assembler. Will need to learn it.
Was thinking of using /bin/perl or /bin/perl5 but that language is only available on OS4.2. That is definately a 90s language, I remember it being all the rage in the 90s for making dynamic webpages.
I could write a small ANSI C89 programme but then users would need to have installed the developer package as well, which I'm guessing most users on this forum would have installed.
Title: Re: Default app for checksums with standard install?
Post by: pTeK on June 19, 2024, 05:03:31 AM
Post by: pTeK on June 19, 2024, 05:03:31 AM
Uggghh so I've converted the hexadecimal PCI identifiers to octal and now I don't know how to search for them in the binary file EIDE_reloc (v 3.37).
All the posts of similar questions on stackoverflow and unix.stackexchange.com all use flags in modern grep or sed that don't exist on Nextstep 3.3 stock install ;D .
I can get the offsets by using the hex editor Hexi (C) 1994 Tobias Hoellrich.
$c4c, $87ac, $8854, $8ed8
But if any one knows how to search for binary strings in a binary file some pointers would be much appreciated, trying to do this without chat gpt.
EDIT: I'll be using /bin/dd to split the file like @stepleton mentioned above, I just wanted to know if there was some stock command that could be searched for binary strings in binary files, even the dreaded octal is better than nothing.
All the posts of similar questions on stackoverflow and unix.stackexchange.com all use flags in modern grep or sed that don't exist on Nextstep 3.3 stock install ;D .
I can get the offsets by using the hex editor Hexi (C) 1994 Tobias Hoellrich.
$c4c, $87ac, $8854, $8ed8
But if any one knows how to search for binary strings in a binary file some pointers would be much appreciated, trying to do this without chat gpt.
EDIT: I'll be using /bin/dd to split the file like @stepleton mentioned above, I just wanted to know if there was some stock command that could be searched for binary strings in binary files, even the dreaded octal is better than nothing.